AWS Direct Connect is a network service that provides an alternative to using the Internet to connect a customer’s on-premises sites to AWS.
Data is transmitted through a private network connection between AWS and a customer’s datacenter or corporate network.
Benefits:
- Reduce cost when using large volumes of traffic.
- Increase reliability (predictable performance).
- Increase bandwidth (predictable bandwidth).
- Decrease latency.
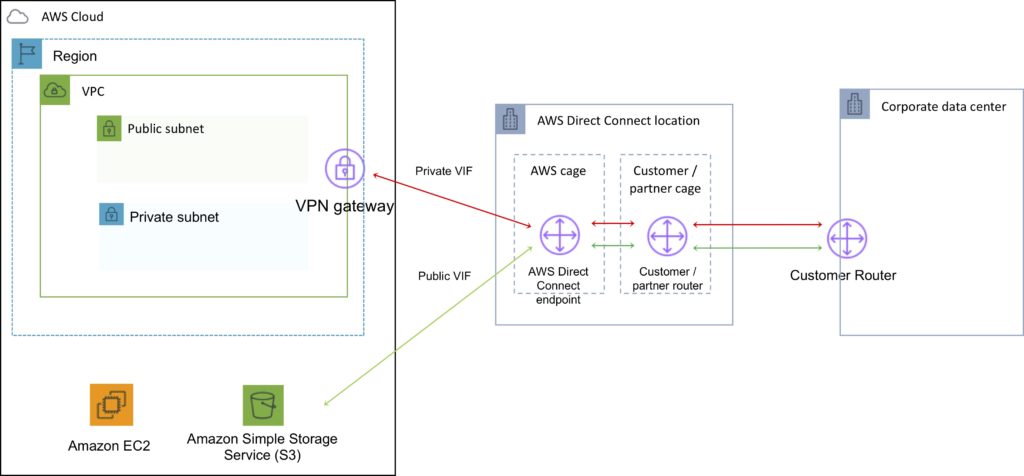
Each AWS Direct Connect connection can be configured with one or more virtual interfaces (VIFs).
Public VIFs allow access to public services such as S3, EC2, and DynamoDB.
Private VIFs allow access to your VPC.
Must use public IP addresses on public VIFs.
Must use private IP addresses on private VIFs.
Cannot do layer 2 over Direct Connect (L3 only).
From Direct Connect you can connect to all AZs within the region.
You can establish IPSec connections over public VIFs to remote regions.
Route propagation can be used to send customer side routes to the VPC.
You can only have one 0.0.0.0/0 (all IP addresses) entry per route table.
You can bind multiple ports for higher bandwidth.
Virtual interfaces are configured to connect to either AWS public services (e.g. EC2/S3) or private services (e.g. VPC based resources).
The diagram below shoes the components of AWS Direct Connect:
Direct Connect is charged by port hours and data transfer.
Available in 1 Gbps, 10 Gbps, and 100 Gbps (limited Regions).
Speeds of 50 Mbps, 100 Mbps, 200 Mbps, 300 Mbps, 400 Mbps, and 500 Mbps can be purchased through AWS Direct Connect Partners (APN Partners).
Uses 802.1q VLANs.
Each connection consists of a single dedicated connection between ports on the customer router and an Amazon router.
for HA you must have 2x DX connections – can be active/active or active/standby.
Route tables need to be updated to point to a Direct Connect connection.
VPN can be maintained as a backup with a higher BGP priority.
Recommended to enable Bidirectional Forwarding Detection (BFD) for faster detection and failover.
You cannot extend your on-premises VLANs into the AWS cloud using Direct Connect.
Can aggregate up to 4 Direct Connect ports into a single connection using Link Aggregation Groups (LAG).
AWS Direct Connect supports both single (IPv4) and dual stack (IPv4/IPv6) configurations on public and private VIFs.
Technical requirements for connecting virtual interfaces:
- A public or private ASN. If you are using a public ASN you must own it. If you are using a private ASN, it must be in the 64512 to 65535 range.
- A new unused VLAN tag that you select.
- Private Connection (VPC) – The VPC Virtual Private Gateway (VGW) ID.
- Public Connection – Public IPs (/30) allocated by you for the BGP session.
AWS Direct Connect does not offer encryption.
You can encrypting data sent over DX by establishing a VPN tunnel over the DX connection.
- Running an AWS VPN connection over a DX connection provides consistent levels of throughput and encryption algorithms that protect your data.
- Though a private VIF is typically used to connect to a VPC, in the case of running an IPSec VPN over the top of a DX connection it is necessary to use a public VIF.
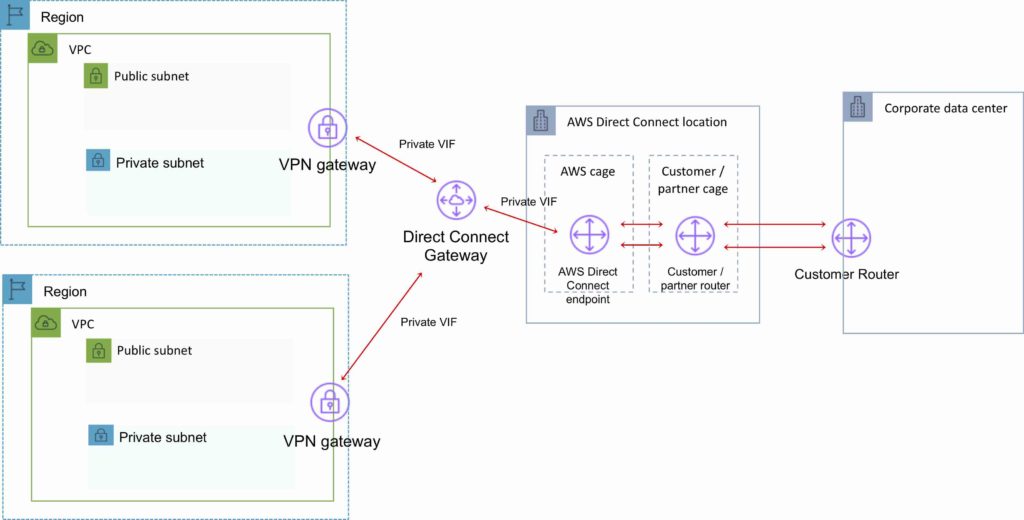
AWS Direct Connect Gateway
Grouping of Virtual Private Gateways (VGWs) and Private Virtual Interfaces (VIFs) that belong to the same AWS account.
Direct Connect Gateway enables you to interface with VPCs in any AWS Region (except AWS China Region).
You associate an AWS Direct Connect gateway with either of the following gateways:
- A transit gateway when you have multiple VPCs in the same Region.
- A virtual private gateway.
Can share private virtual interface to interface with more than one Virtual Private Clouds (VPCs) reducing the number of BGP sessions.
A Direct Connect gateway is a globally available resource.
You can create the Direct Connect gateway in any public Region and access it from all other public Regions.
The diagram below depicts the components of an AWS Direct Connect Gateway configuration: